Discover
Vulnerability Research, Exploit Intelligence
Finding and analyzing 0-day vulnerabilities is our first passion and primary occupation. We offer our auditing services for organizations that look for outside help in assessing the security of a product. We can help you scan your codebase for vulnerabilities or focus on exploitability analysis and proof-by-construction. Our methodology is geared towards uncovering high impact issues and identifying changes that can make a stronger impact than point fix bug squashing. In addition, we continuously focus on public vulnerability research in our domain. You can rely on our intelligence reports if you need help determining the effect of a new exploit or attack technique on your bottom line.
Recover
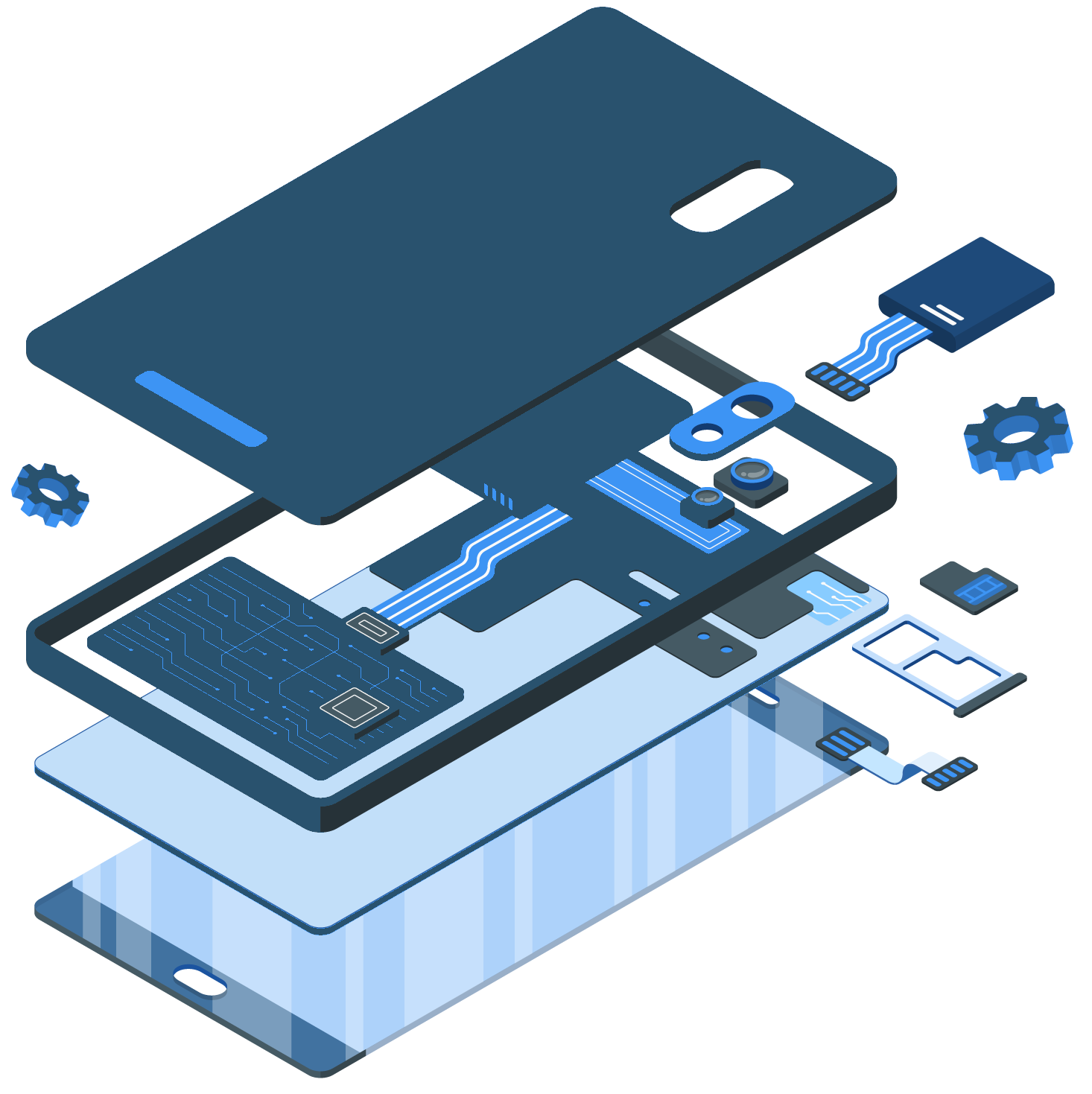
Mobile Forensics, Incident Response
Malware and intrusion detection is a huge and booming market. We don’t bring one more AV product to it. Instead, our focus is on custom projects where data recovery and extraction or intrusion attempt analysis is a challenge for available commercial offerings. Our low-level familiarity with smartphone system-on-chip designs in particular has helped us come to the rescue time and again. We also bring our proprietary tools and unique expertise in Software-Defined Radios to the challenges associated with the capture, detection, and analysis of rogue radio network traffic.
Fortify
Secure Software and Hadware Development
Our team has many years of experience in secure development practices, from threat modelling and countermeasure design to secure programming. We have guided and audited countless projects and assisted in the development of SDLC frameworks in various organizations in both the private and public sectors. First and foremost, we feel at home with low-level development projects.
Verify
Security Assessment, Reverse Engineering
Not every scenario allows for a whitebox review. This is especially true in the embedded, automotive, and mobile industries, where long chains of suppliers often result in complicated ownership combinations of various firmware components. In these cases, binary reverse engineering can bring powerful results. Beyond de-facto standard reverse engineering tools, we also regularly deal with cases where COTS tooling solutions don’t exist, due to proprietary OSes, file formats, or CPU architectures.
Educate
Security Trainings & Advisories
Our “tailored to fit” philosophy is reflected in our approach to offering security trainings as well. In previous roles, we have experienced first hand the frustration that “once size fits all” offerings can cause when expectation meets the reality of the limited use for the audience. We have the experience of developing customized trainings and have perfected our delivery skills through hundreds of hours of private security trainings. Reach out if you are looking for a training for your team that will really be fit for purpose.
Initiate
Rapid Prototyping
Hacking for us means more than popping shells. Since the days of fiddling with bits and wires in a hackerspace, we have loved building things as much as breaking them. We like to say that we are hackers in the original sense of the word and this is why we proudly offer rapid prototyping services as well. Our diverse team includes electrical and mechanical engineers by trade. We have many years of hands-on experience with Radio Access Technologies and SDR-based development in particular. If your vision includes bits in the air - we can turn it into reality for you!